写在前面
你是否被reverse中的神必加密小程序搞得神志不清?
你是否读懂了加密代码后却对解密无从下手?
反正我这几天是被折磨不轻了,遂决定从密码学中学习一点皮毛以缓解痛楚。
之后会在一直更,但这两个月大概率不怎么会更了,安心准备转专业考试
第一章
Cryptography, the methodology of concealing the content of messages, comes from the Greek root words kryptos, meaning hidden,and graphikos, meaning writing. The modern scientific study of cryptography is sometimes referred to as cryptology.
1. Caesar cipher
操作:每个字母都被替换
总体来说,他属于一种大的类型——替换密码
由于这样子看稍费一点脖子,于是整理成表:
2. one-to-one or injective
跟函数一样,即有加密函数中两个明文字母不会同时指向同一个密文字母
顺着凯撒密码的思路,也就是说,我们可以瞎几把乱对映(a->26个字母中的任意一个,以此类推)得出有26·25·24…·1=26!种方法,将26个明文字母分配给26个密文字母。
也就是说,面对这种东西的时候,你得有策略,想方设法去做。
Your opponent always uses her best strategy to defeat you, not the strategy that you want her to use. Thus the security of an encryption system depends on the best known method to break it. As new and improved methods are developed, the level of security can only get worse, never better.
eg:习惯法,我第一次见到是在福尔摩斯来着
To take an extreme example, the letter q in English is virtually always followed by the letter u. More useful is the fact that certain letters such as e and t appear far more frequently than other letters such as f and c. Table lists the letters with their typical frequencies in English text. As you can see, the most frequent letter is e, followed by t, a, o, and n.
通过对加密的消息制作频率表,便可以迅速确定e,再通过e展开去推断
A simple substitution cipher to cryptanalyze:
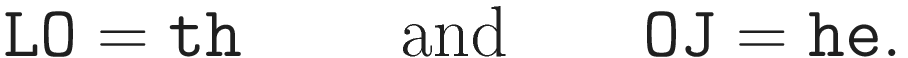
LOJUM YLJME PDYVJ QXTDV SVJNL DMTJZ WMJGG YSNDL UYLEO SKDVC
GEPJS MDIPD NEJSK DNJTJ LSKDL OSVDV DNGYN VSGLL OSCIO LGOYG
ESNEP CGYSN GUJMJ DGYNK DPPYX PJDGG SVDNT WMSWS GYLYS NGSKJ
CEPYQ GSGLD MLPYN IUSCP QOYGM JGCPL GDWWJ DMLSL OJCNY NYLYD
LJQLO DLCNL YPLOJ TPJDM NJQLO JWMSE JGGJG XTUOY EOOJO DQDMM
YBJQD LLOJV LOJTV YIOLU JPPES NGYQJ MOYVD GDNJE MSVDN EJM
这个时候,我的话就直接让AI分析频率了,
不过这些倒是直接偷的书上的
然后是两个字的频率
具体的过程看原书就是了
Some information may be outdated